42Crunch Platform release, April 9, 2026
|
Platform version: v1.55.x |
This 42Crunch API Security Platform release brings mutual TLS (mTLS) support to API Scan v2 and lets you run it in 42Crunch Platform.
New features
The following are the new features and improvements to the existing ones in this release.
Improvements to Scan v2
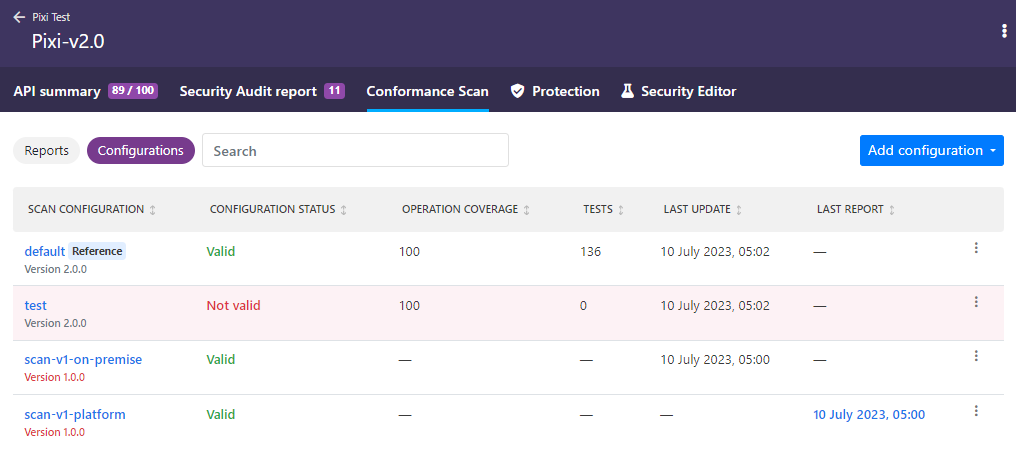
You can now run any Scan v2 configuration either in 42Crunch Platform or on premises, whichever suits your needs. For each configuration, the latest report is stored and you can see where each configuration was last run.
Some scan runtime settings are capped at a lower level than what is specified in the scan configuration when the scan is run on the platform. For more details, see API Scan settings.
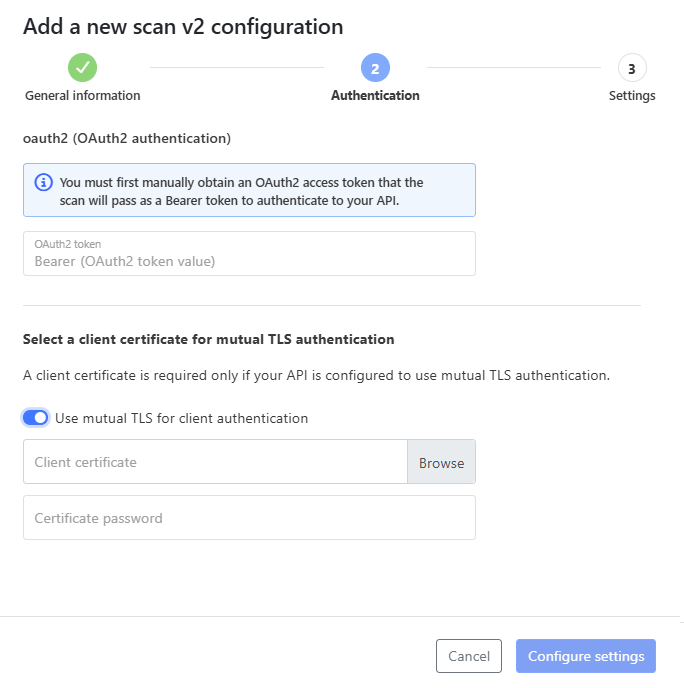
Scan configuration for Scan v2 now have a similar wizard on the UI that lets you provide some details, such as authentication information and runtime settings already when creating the scan configuration. Advanced features of the Scan v2 configurations, such as scenarios or environment variables, are not available in the wizard and must be edited separately after creating the configuration.
Scan v2 now also support mutual TLS (mTLS) as an authentication method and you can provide the required details for it the same way as for Scan v1.
We have also fixed the value generation for oneOf schemas with multiple accepted object types.
Fore more details, see Use API Scan v2 engine.
Improvements to GraphQL support
If the authentication of your GraphQL API requires passing multiple HTTP headers, you can now include multiple security schemes in the scan configuration to cover all the required headers.
We have also switched the from structural pointers for where issues were discovered in the GraphQL API definition to absolute location pointers. As JSON pointers are not supported in GraphQL, absolute location pointers are a better and more reliable replacement.
We have also fixed several bugs related to GraphQL:
- Improved some confusing texts in audit issues when using the GraphQL Java Extended Validation framework
- Improved the handling of valid empty input objects during scan
- Increased the maximum allowed length for returned responses before raising an issue on excessive details
Support for GraphQL is not enabled by default, but is available as a separate subscription. If you are interested in adding GraphQL support to your subscription, contact sales@42crunch.com.
GraphQL is not yet supported in API Protection, CI/CD plugins, data dictionaries, or API Contract Generator.
Improvements to the OpenAPI Specification (OAS) v3.1.x support in Security Audit
The full support of JSON Schema Validation brings new keywords to the OAS v3.1.x that can be used in OpenAPI definitions.
- Security Audit now acknowledges these new keywords (such as
contains,unevaluatedItems) as valid part of OpenAPI definitions. - You can now use the conditional keywords
if,then, andelseto describe conditional logic in your API definition - We have also implemented new checks for the keyword
const(short of constant:
Bulk deletion of API collections
You can now delete multiple API collections and the APIs in them at one go. Simply tick the boxes of the collections you want to delete and then click the Delete button above the list.
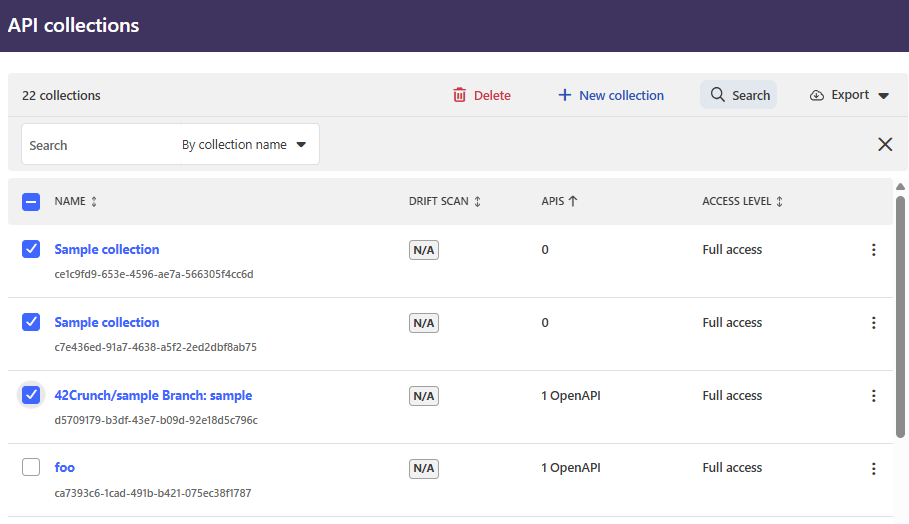
If some of the collections or APIs in them cannot be deleted, for example, because of active API Firewall instances running or you do not have the permission to delete them, you will be notified about those and can still proceed to delete the rest of the selected collections.
For more details, see Manage API collections.
Compatibility
This section lists the compatible Docker images for some of the components of 42Crunch API Security Platform, as well as other possible compatibility details.
API Firewall images
This release is compatible with the following API Firewall images:
- NEW:
42crunch/apifirewall:v1.2.3- Upgrade to
go-1.26.1
- Upgrade to
We highly recommend that you switch to the latest image version to take full advantage of the new features and security improvements.
-
42crunch/apifirewall:v1.2.2- Upgrade to
go-grpc 1.79.3(CVE-2026-33186) - Fixed a regression in handling the keyword
nullable - Upgrade to
go-1.25.8(CVE-2026-27142, CVE-2026-25679) - Upgrade to
go-grpc 1.79.0
- Upgrade to
42crunch/apifirewall:v1.2.0- Support for the OAS v3.1
- Upgrade to
go-1.25.6(CVE-2025-68121, CVE-2025-61728, CVE-2025-61726, CVE-2025-61731, CVE-2025-68119) - Upgrade to
openssl 3.5.5(CVE-2025-11187, CVE-2025-15467, CVE-2025-15468, CVE-2025-15469, CVE-2025-66199, CVE-2025-68160, CVE-2025-69418, CVE-2025-69419, CVE-2025-69420, CVE-2025-69421, CVE-2026-22795, CVE-2026-22796)
-
42crunch/apifirewall:v1.1.16- Upgrade to
httpd-2.4.66(CVE-2025-55753, CVE-2025-58098, CVE-2025-59775, CVE-2025-65082, CVE-2025-66200) - Upgrade to
golang-1.25.5(CVE-2025-61727, CVE-2025-61729)
- Upgrade to
42crunch/apifirewall:v1.1.15- Upgrade to
PCRE2-10.46(CVE-2025-58050)
- Upgrade to
-
42crunch/apifirewall:v1.1.14- Upgrade to
openssl-3.5.4(CVE-2025-9230, CVE-2025-9231, CVE-2025-9232) - Upgrade to
libexpat-2.7.3(CVE-2025-59375) - Upgrade to
go-1.25.3(CVE-2025-61724, CVE-2025-58187, CVE-2025-47912, CVE-2025-58183, CVE-2025-61723, CVE-2025-58186, CVE-2025-58185, CVE-2025-58188, CVE-2025-61725)
- Upgrade to
42crunch/apifirewall:v1.1.13- Upgrade to
httpd-2.4.65(CVE-2025-53020, CVE-2025-49812, CVE-2025-49630, CVE-2025-23048, CVE-2024-47252, CVE-2024-43394, CVE-2024-43204, CVE-2024-42516, CVE-2025-54090)
- Upgrade to
42crunch/apifirewall:v1.1.12- Fixed handling of schema validating errors
- Upgrade to
go-1.24.4(CVE-2024-45338) - Upgrade to
go-grpc 1.73.0
-
42crunch/apifirewall:v1.1.11- Fixed resource consumption on graceful restart
-
42crunch/apifirewall:v1.1.9- Upgrade to
expat 2.7.0-r0(CVE-2024-8176) - Upgrade to
golang.org/x/net 0.36.0(CVE-2025-22870)
- Upgrade to
42crunch/apifirewall:v1.1.8- Upgrade to
openssl-3.3.3(CVE-2024-12797, CVE-2024-13176)
- Upgrade to
42crunch/apifirewall:v1.1.7- Fixed the failure in forwarding large request bodies
- Upgrade to
go-1.23.4(CVE-2024-45338)
-
42crunch/apifirewall:v1.1.6- Upgrade to
openssl-3.3.2-r1(CVE-2024-9143)
- Upgrade to
42crunch/apifirewall:v1.1.5- Switch to the system certificate store to fix certificate authority renewal issue
All previous image versions have been deprecated and are no longer supported. We highly recommend that you switch to the latest image version to take the full advantage of the new features and security improvements.
When you switch the version of the API Firewall image, you must reconfigure any existing protection configurations so that they work with the new version. For more details, see Reconfigure API Protection.
API Scan images
This release is compatible with the following API Scan images for running it on-premises. The major release number indicates if the image is for Scan v1 or Scan v2 engine.
Scan v2
- NEW:
42crunch/scand-agent:v2.55.1- Upgrade to
Golang 1.26.2(CVE-2026-32280, CVE-2026-32281, CVE-2026-32282, CVE-2026-32283, CVE-2026-32288, CVE-2026-32289, CVE-2026-33810) - Fixed running of all scan types
- Upgrade to
- NEW:
42crunch/scand-agent:v2.55.0- Fixed value generation for
oneOfschemas with multiple accepted object types - Fixed handling of empty input objects in GraphQL APIs
- Increased maximum length of returned responses for GraphQL APIs
- Fixed value generation for
We highly recommend that you switch to the latest image version to take full advantage of the new features and security improvements.
42crunch/scand-agent:v2.54.2- Upgrade to
google.golang.org/grpc v1.79.3(CVE-2026-33186) - Improvements to GraphQL support
- Upgrade to
Golang 1.26.1(CVE-2026-25679, CVE-2026-27137, CVE-2026-27138, CVE-2026-27139, CVE-2026-27142)
- Upgrade to
42crunch/scand-agent:v2.53.2- Upgrade to
google.golang.org/grpc v1.79.3(CVE-2026-33186)
- Upgrade to
42crunch/scand-agent:v2.53.1- Fix to scan runtime settings
42crunch/scand-agent:v2.53.0- Fixed value generation on conformance tests
- Upgrade to
Golang 1.25.6(CVE-2025-61726, CVE-2025-61728, CVE-2025-61730)
42crunch/scand-agent:v2.52.0- Upgrade to
golang.org/x/crypto v0.45.0(CVE-2025-47914, CVE-2025-58181)
- Upgrade to
42crunch/scand-agent:v2.51.0- Upgrade to
golang.org/x/crypto v0.44.0(CVE-2025-47913) - Fixed including nested objects in arrays in requests
- Upgrade to
42crunch/scand-agent:v2.50.2- Upgrade to
Golang 1.25.3(CVE-2025-58185) - Adjusted proxy behavior
- Fixed handling of examples in test generation
- Upgrade to
42crunch/scand-agent:v2.50.0- Upgrade to
Golang 1.25.1(CVE-2025-47906) - Fixed generating a value for a test in case of an overflow
- Fixed calculation of estimated tests in case of skipped tests
- Fixed parsing error with long strings of numbers
- Upgrade to
42crunch/scand-agent:v2.49.0- Support for drift scan
42crunch/scand-agent:v2.48.0- Ignore unsupported operations during scan
- Fixed calculation of estimated tests and executed tests
- Fixed variable replacement in Scan v2 in v1-compatible mode
42crunch/scand-agent:v2.47.0- Ignore unsupported methods
X-Scan-Transactionidincluded in every request- Upgrade to
chi v5.2.2(CWE-601)
42crunch/scand-agent:v2.46.3- Upgrade to
Golang 1.24.4(CVE-2025-0913, CVE-2025-22874, CVE-2025-4673)
- Upgrade to
42crunch/scand-agent:v2.46.1- Scan rules defined in the platform taken into account in scans
- URL normalization
42crunch/scand-agent:v2.45.0- Upgrade to
Golang 1.24.2(CVE-2025-22871) - Upgrade to
golang.org/x/net v0.39.0(CVE-2025-22872)
- Upgrade to
All previous image versions have been deprecated and are no longer supported.
Scan v1
- NEW:
42crunch/scand-agent:v1.55.1- Upgrade to
Golang 1.26.2(CVE-2026-32280, CVE-2026-32281, CVE-2026-32282, CVE-2026-32283, CVE-2026-32288, CVE-2026-32289, CVE-2026-33810)
- Upgrade to
- NEW:
42crunch/scand-agent:v1.55.0- Internal cleanup and refactoring
We highly recommend that you switch to the latest image version to take full advantage of the new features and security improvements.
- NEW:
42crunch/scand-agent:v1.54.2- Upgrade to
google.golang.org/grpc v1.79.3(CVE-2026-33186) - Upgrade to
Golang 1.26.1(CVE-2026-25679, CVE-2026-27137, CVE-2026-27138, CVE-2026-27139, CVE-2026-27142)
- Upgrade to
42crunch/scand-agent:v1.53.2- Upgrade to
google.golang.org/grpc v1.79.3(CVE-2026-33186)
- Upgrade to
42crunch/scand-agent:v1.53.1- Fix to scan runtime settings
42crunch/scand-agent:v1.53.0- Upgrade to
Golang 1.25.6(CVE-2025-61726, CVE-2025-61728, CVE-2025-61730)
- Upgrade to
-
42crunch/scand-agent:v1.52.0- Upgrade to
golang.org/x/crypto v0.45.0(CVE-2025-47914, CVE-2025-58181)
- Upgrade to
42crunch/scand-agent:v1.51.0- Upgrade to
golang.org/x/crypto v0.44.0(CVE-2025-47913) - Fixed including nested objects in arrays in requests
- Upgrade to
-
42crunch/scand-agent:v1.50.2- Upgrade to
Golang 1.25.3(CVE-2025-58185) - Adjusted proxy behavior
- Upgrade to
42crunch/scand-agent:v1.50.0- Upgrade to
Golang 1.25.1(CVE-2025-47906)
- Upgrade to
42crunch/scand-agent:v1.49.0- Internal cleanup and refactoring
42crunch/scand-agent:v1.48.0- Fixed scan report size checks
42crunch/scand-agent:v1.47.0- Ignore unsupported HTTP methods
X-Scan-Transactionidincluded in every request- Upgrade to
chi v5.2.2(CWE-601)
-
42crunch/scand-agent:v1.46.3- Upgrade to
Golang 1.24.4(CVE-2025-0913, CVE-2025-22874, CVE-2025-4673)
- Upgrade to
42crunch/scand-agent:v1.46.0- Internal cleanup and refactoring
42crunch/scand-agent:v1.45.0- Upgrade to
Golang 1.24.2(CVE-2025-22871) - Upgrade to
golang.org/x/net v0.39.0(CVE-2025-22872)
- Upgrade to
All previous image versions have been deprecated and are no longer supported.
Changed behavior
- Security Audit no longer flags the new keywords brought by the full JSON Schema Validation support as unrecognized properties. Depending on your API, this may affect the validity of your API definition.
- Security Audit now raises new issues on the keyword
const. Depending on your API, this may affect the validity of your API. - As the location pointers in audit reports for GraphQL APIs have changed, you may need to rerun Security Audit before you can open the report on the UI.
Deprecated components
The following have been deprecated and will be removed in the future.
Deprecated features
Scan v2 in v1-compatible mode has been deprecated, as Scan v2 now offers the same capabilities, and more.
Any existing scan configurations for the v1-compatible mode are retained and you can continue to use them. However, you can no longer create new scan configurations for the v1-compatible mode. Use Scan v2 instead.
Deprecated API endpoints
The following API endpoints in 42Crunch Platform related to Scan v2 in v1-compatible mode have been marked as deprecated and will be removed in the future:
/api/v2/apis/{id}/scanConfigurations/compatibility
Known issues
This release has the following known issues.
Manage teams permission not shown on list of users
The permission to manage teams is not yet shown on the list of users in your organization, but you can view all permissions that a user has by clicking the permission column. This permission also does not yet have a shortcut that you could use when searching by permission.
These will be fixed in a future release.
Changing tagging on an API may trigger an unrelated error on the UI
Sometimes applying tags to or removing them from an API may trigger an unrelated error on failing to fetch the SQG approval report for the API. This happens if the API in question has been scanned on-premises and the scan has finished after you arrived on the API Summary page, because the UI cannot find the latest on-premises scan report and the associated approval report. Refreshing the page gets the latest reports and resolves the issue.
Tagging and untagging the API is not affected by this error: tags get correctly applied and removed in any case.
This will be fixed in a future release.
Data dictionary duplication
Duplicating a data dictionary does not yet duplicate the values in it.
This will be fixed in a future release.
Scan customization rules may lead to no response codes being accepted.
In some cases, scan rules can lead to HTTP status response codes in API responses that are normally expected (for example, HTTP 401 or HTTP 404) to be treated as unexpected. This in turn can lead to a false positive in the scan results.
By default, the expected HTTP status response codes that are defined in scan rules applied to the scanned API take preference over the response codes that API Scan would otherwise expect. However, this can cause problems in scan process if your scan rule only skips header or response body analysis but does not define any expected response codes, either for happy path requests or for particular test IDs. This results in the scan rule to have null defined as the expected response code, and because the scan rule takes preference over the default scan behavior, no response codes except null are accepted. This in turn means that some tests are incorrectly flagged as returning unexpected response codes when they were in fact successful.
We are currently investigating the best way how to reconcile the designed behavior of API Scan and scan rules in these cases, and this issue will be fixed in a future release.