Integrate Security Audit with Jenkins
You can integrate API Security Audit with Jenkins pipelines through the plugin REST API Static Security Testing.
You must have an account in 42Crunch Platform that your Jenkins job can use to access Security Audit. Currently, GraphQL APIs are not supported.
Before you start, make sure that your Jenkins version is the same or newer than the minimum compatible version. If you are installing the integration plugin manually, not using the Update Center, make sure that you also install the dependencies.
For more details on Jenkins, see Jenkins User Documentation.
Security Audit is integrated through a plugin that adds a build task or job to your CI/CD pipeline. The plugin checks the quality of the OpenAPI files present in your project. If the detected APIs do not meet the criteria you define in the plugins or in your security quality gates in 42Crunch Platform, the plugin fails and aborts the build, so that bad APIs are not included in your project.
The process has two phases:
- Discovery: The task in your CI/CD pipeline checks your project for any
.json,.yaml, and.ymlfiles. When it finds a file, it checks if the file states that it is an OpenAPI file. If the file is.yamlor.yml, it is automatically converted to JSON. The discovered APIs are automatically uploaded to an API collection in 42Crunch Platform. - Audit: Security Audit audits the uploaded APIs for their well-formedness and security. If the quality of the APIs meets your criteria, the task or job ends with a success, if they do not, the task fails. Your CI/CD pipeline processes the result as you have defined and the continues to the next task or job.
The plugin uses API tokens with specific access rights (scopes) to access 42Crunch Platform.
When the integration plugin runs, it uploads the API definitions it finds during the discovery phase to a particular API collection in your organization in 42Crunch Platform. By default when running on branch, the plugin uses the naming convention <shortened-source-control-uri> Branch:<branch-name> for the created API collection, for example, 42Crunch/sample Branch:sample.
On subsequent runs, the plugin synchronizes the contents of the API collection with the APIs in your source control repository:
- APIs added to your repository are added to the collection.
- APIs removed from your repository are removed from the collection
- APIs found both in your repository and in the collection retain their API UUIDs in 42Crunch Platform but their contents are replaced with the contents of the files in your repository
Make sure that you do not accidentally overwrite things in the API definition that you would like to keep. The plugin will replace all contents in the APIs in 42Crunch Platform with the contents of the API files in your repository. Any changes that are not reflected in the OpenAPI file in your repository are lost from the platform.
Create an API token for the Jenkins job
You must add an API token that the Jenkins job uses to authenticate to Security Audit.
- Log in to 42Crunch Platform, and click next to your username.
- Select Tokens, and click Create new token.
- Enter a unique and descriptive name for the token, such as
Security Audit token. - Make sure the token type is API token, and in token access rights, select API Security Audit, List resources, and Delete resources.
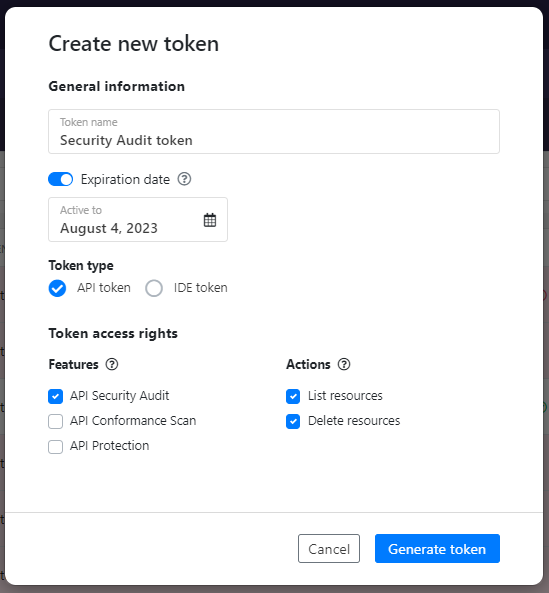
- Click Generate token.
- Copy the token value, you will need it when you configure REST API Static Security Testing.
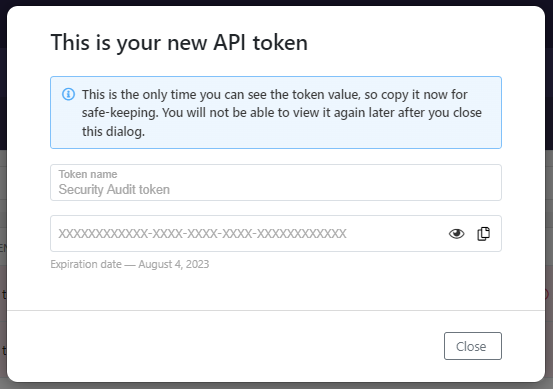
Add the API token in Jenkins credentials
Before you add the task to your Jenkins job, you must install the plugin and add the API token you created to your Jenkins credentials.
Installing the integration plugin also installs the credential type that the plugin uses for authentication, and in most cases no action is needed from you. However, if you have chosen to use credential types selectively on your Jenkins, you must enable this credential type for the plugin to work. After you have installed the plugin, go to Manage Jenkins > Configure Credential Providers, and make sure that the credential type 42Crunch API Token is enabled.
- Log in to your Jenkins account.
- If your Jenkins server does not yet have the REST API Static Security Testing plugin installed, install it from Jenkins Update Center. This needs to be done only once for each Jenkins server.
- Go to Manage Jenkins > Manage Credentials.
- Go to the domain you want and click Add Credentials.
- Set the following:
- Kind: Select 42Crunch API Token.
- ID: Enter a name for the credential. If you configure the Jenkins job using
Jenkinsfile, this is the value you will use. - Description: Enter a description for the credential. If you configure the Jenkins job on the UI, this is the value you will use.
- API Token: Enter the value of the API token you created for the Jenkins job.
- Click OK.
The API token is added to your Jenkins credentials, and you can use it when you configure your Jenkins job.
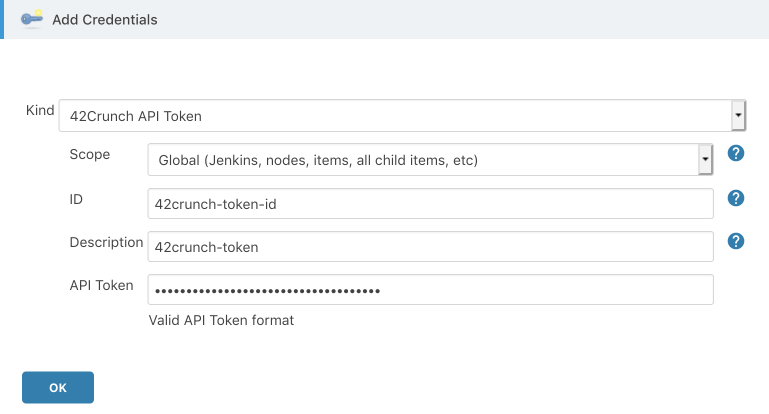
Configure the Jenkins job
To integrate Security Audit with Jenkins, you must configure a build step in your Jenkins job.
You can log into your Jenkins account, and configure the settings for the integration on the Jenkins UI.
- Open the Jenkins job that you want to integrate with API Security Audit.
- Go to the Build phase, and add a step called API Security Audit.
- In API Token, select the API token you added to your Jenkins credentials.
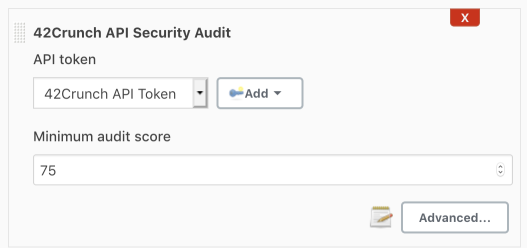
- Enter the minimum audit score that the audited OpenAPI definitions must get from the audit for the build step to succeed. If any API definitions score lower than the minimum score you set, the build step fails. The default is
75.The fail-on criteria you set in the CI/CD plugin, such as the minimum score, are independent from the acceptance criteria defined in security quality gates (SQGs). This means that your CI/CD build can fail either because the criteria of the plugin are not met, the criteria of a SQG are not met, or both.
- If you are an enterprise customer not accessing 42Crunch Platform at
https://us.42crunch.cloud, click Advanced and enter your platform URL. This step is optional and most users do not have to do this. If you are not sure what your platform URL is, contact our support.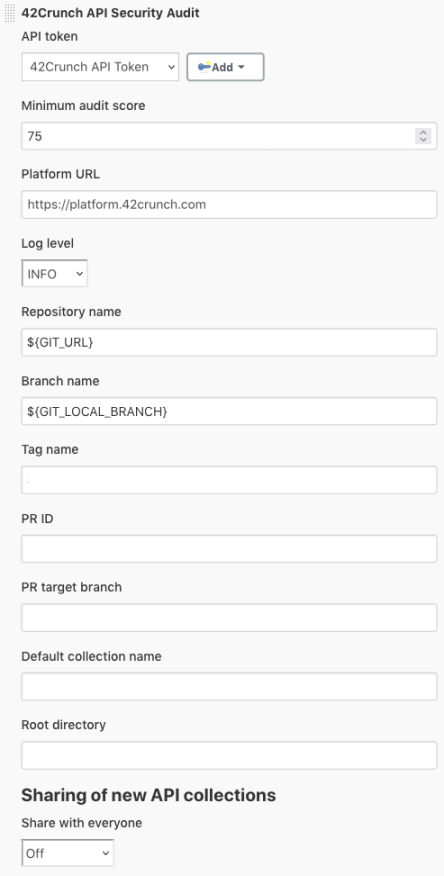
- Set the level of detail (
FATAL,ERROR,WARN,INFO,DEBUG) for the logs that the build step produces. - If you are using other plugins in your Jenkins pipeline, make sure that the build variables match the variables those plugins use.
These variables tell the build step how to name any new API collections it creates in 42Crunch Platform.
- The build variable for the repository is always required. In most cases, the default value
${GIT_URL}is fine. - Depending on how you want to trigger the build, define one of the following:
- To run builds on branches, define the branch name. In most cases, the default value
${GIT_LOCAL_BRANCH}is fine. This is the most common case.If the other plugins in your pipeline use the variable
GIT_BRANCHinstead ofGIT_LOCAL_BRANCH, the resulting branch name usually containsorigin(like inorigin/main) that must be removed. To do this, use the value${env.GIT_BRANCH.replaceFirst(/^.*\//, '')} - To run builds on tags, define the tag name. In most cases, the default value
${TAG_NAME}is fine. - To run builds on PRs, define the PR ID and PR target branch. In most cases, the default values
${CHANGE_ID}and${CHANGE_TARGET}are fine.
- To run builds on branches, define the branch name. In most cases, the default value
- The build variable for the repository is always required. In most cases, the default value
- Select if you want to automatically share any new API collections that the build task creates with other users in your organization (off by default). You can also change the sharing of the API collections later in 42Crunch Platform.
- Click Save to save your changes to the Jenkins job.
If you are using Jenkinsfiles to manage your Jenkins jobs, you can configure the integration directly in a Jenkinsfile.
The REST API Static Security Testing plugin supports both declarative and scripted pipeline syntax. For more details, see Jenkins Pipeline documentation.
- Go to the
Jenkinsfileat the root level of your source code repository where the CI/CD pipeline connects to, and open it for editing. -
Under
stages, add a new stage called, for example,Audit OpenAPI files:stages { ... stage('Audit OpenAPI files') { -
Under your new
stage, add a step calledaudit. This tells your Jenkins job to use the REST API Static Security Testing plugin.stages { ... stage('Audit OpenAPI files') { steps { audit } } ... } - Define build variables that tell the build step how to name any new API collections it creates in 42Crunch Platform. If you are using other plugins in your Jenkins pipeline, make sure that the build variables match the variables those plugins use.
- The build variable
repositoryNameis always required. In most cases, the default value${GIT_URL}is fine. - Depending on how you want to trigger the build, define one of the following:
- To run builds on branches, define
branchName. In most cases, the default value${GIT_LOCAL_BRANCH}is fine. This is the most common case.If the other plugins in your pipeline use the variable
GIT_BRANCHinstead ofGIT_LOCAL_BRANCH, the resulting branch name usually containsorigin(like inorigin/main) that must be removed. To do this, use the value${env.GIT_BRANCH.replaceFirst(/^.*\//, '')} - To run builds on tags, define
tagName. In most cases, the default value${TAG_NAME}is fine. - To run builds on PRs, define
prIdandprTargetBranch. In most cases, the default values${CHANGE_ID}and${CHANGE_TARGET}are fine.
- To run builds on branches, define
stages { ... stage('Audit OpenAPI files') { steps { audit repositoryName: "${env.GIT_URL}", branchName: "${env.GIT_LOCAL_BRANCH}" } } ... } - The build variable
-
To finalize the configuration, specify the following:
credentialsId: The ID you specified for the API token you added to your Jenkins credentials.minScore: The minimum audit score that the audited OpenAPI definitions must get from the audit for the build step to succeed. If any API definitions score lower than the minimum score you set, the build step fails. The default is75.The fail-on criteria you set in the CI/CD plugin, such as the minimum score, are independent from the acceptance criteria defined in security quality gates (SQGs). This means that your CI/CD build can fail either because the criteria of the plugin are not met, the criteria of a SQG are not met, or both.
platformUrl(optional): If you are an enterprise customer not accessing 42Crunch Platform athttps://us.42crunch.cloud, enter the URL you use to access the platform. This step is optional and most users do not have to do this. If you are not sure what your platform URL is, contact our support.logLevel(optional): By default, the level of detail in the logs that the build step produces isINFO. If you want more or less detail, you can change it here. The possible values areFATAL,ERROR,WARN,INFO,DEBUG.shareEveryone: This variable lets you automatically share any new API collections that the plugin creates with other users in your organization in 42Crunch Platform. The variable has two possible values:READ_ONLYorREAD_WRITE, depending on the access level you want to give to them. If you do not defineshareEveryoneat all, the API collections are not shared and remain private to you. You can also change the sharing of the API collections later. For more details, see Sharing APIs and access level.
stages { ... stage('Audit OpenAPI files') { steps { audit repositoryName: "${env.GIT_URL}", branchName: "${env.GIT_LOCAL_BRANCH}", credentialsId: '42crunch-token-id', minScore: 75, platformUrl: 'https://<your platform URL here>', logLevel: 'DEBUG' } } ... } - Save your changes to the
Jenkinsfile.
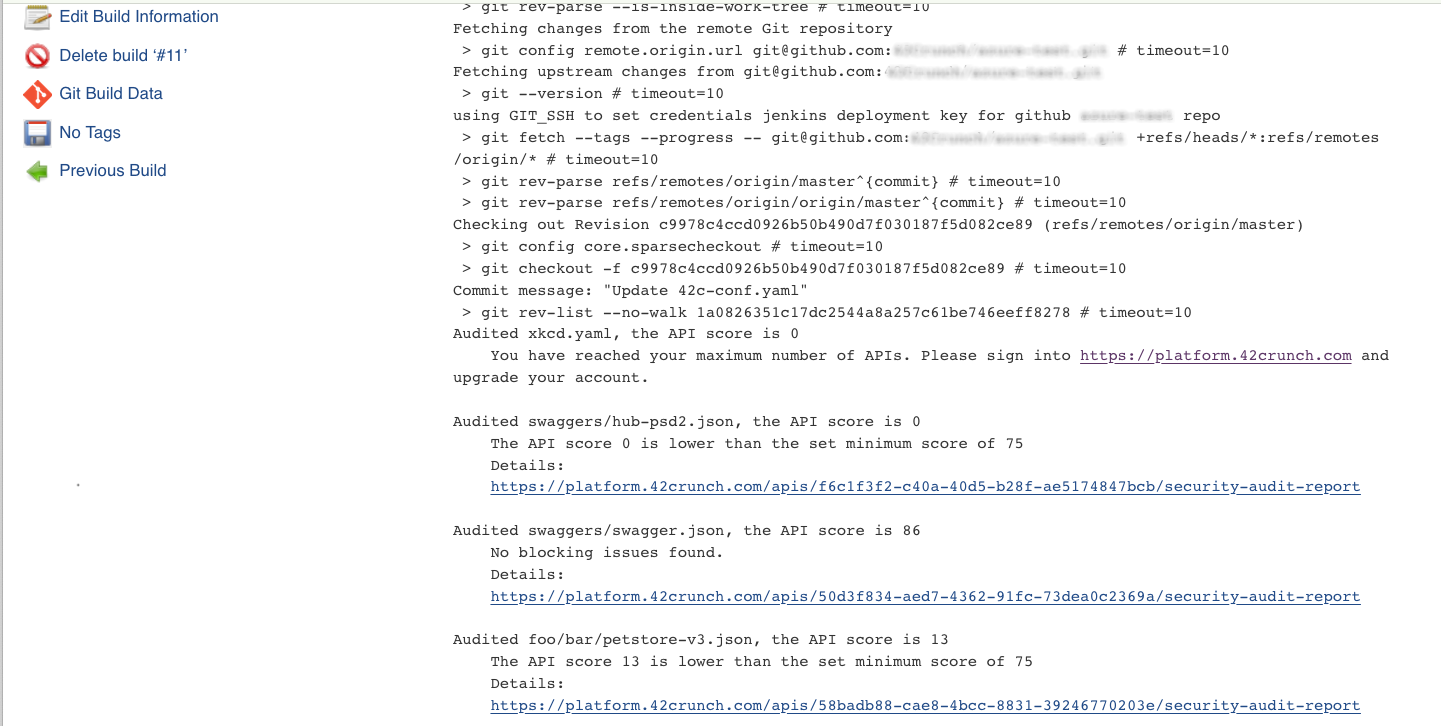
To test integration, run your Jenkins pipeline. The build step will either succeed or fail depending on the minimum score. The plugin also automatically checks the status of all SQGs applied to the APIs it found in the repository. If any of the SQGs fails, the build automatically fails too. The summary of the run in the pipeline jobs provides you further details how the job went.
The build step uploads all discovered OpenAPI definitions to the specified API collection in 42Crunch Platform. By default when running on branch, the plugin uses the naming convention <shortened-source-control-uri> Branch:<branch-name> for the created API collection, for example, 42Crunch/sample Branch:sample.
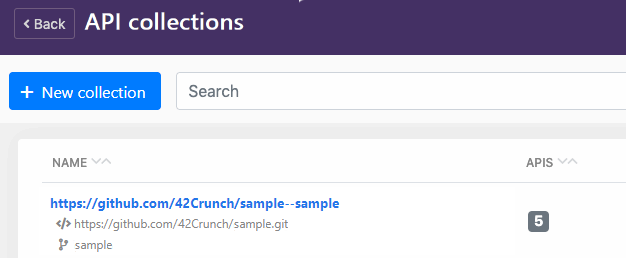
The API definitions in the collection show the filepaths they have in the repository:
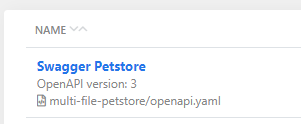
The logs of the run include the URL of each discovered API in the platform. You can copy the URL and paste it to your browser to view the detailed audit report of the corresponding API.
Write summary of the plugin run in a file
If you want, you can set the plugin to write and store a report on the plugin run as a JSON file, so that it is easy, for example, to see and communicate the API UUIDs of the uploaded APIs.
This is not the audit report that provides details on the issues that Security Audit found in your APIs and how to remediate them, but a separate, optional summary providing some basic details on the APIs that the plugin processed. The full audit reports are not included in this summary, but are available in 42Crunch Platform.
- Go to the Jenkins job you want and open the settings of the integration plugin for editing.
- In Write JSON report to, enter the filename or path that you want to use for report file.
The report is in JSON format, so ensure that you either specify
.jsonas the file extension (as intest/myReport.json) or omit the extension completely (test/myReport).- If you specify only the filename, the plugin creates the file in the root directory that it is pointed to start from.
- If you specify a path, the path must be under the root directory and all specified directories must exist. The plugin only generates the JSON file, not directories.
The plugin does not delete or overwrite any summaries from previous runs, so if a file with the same name exists, you see an error. To avoid this, you can create a separate workspace for each pipeline pass, add a task to clear the workspace before starting, or include a variable to the filename (such as the build number or timestamp) to ensure that each filename is unique.
- Save your changes.
- Go to the
Jenkinsfileyou want, and open it for editing. - Add the build variable
jsonReportto the audit stage, and, enter the filename or path that you want to use for report file. The report is in JSON format, so ensure that you either specify.jsonas the file extension (as intest/myReport.json) or omit the extension completely (test/myReport).- If you specify only the filename, the plugin creates the file in the root directory that it is pointed to start from.
- If you specify a path, the path must be under the root directory and all specified directories must exist. The plugin only generates the JSON file, not directories.
The plugin does not delete or overwrite any summaries from previous runs, so if a file with the same name exists, you see an error. To avoid this, you can create a separate workspace for each pipeline pass, add a task to clear the workspace before starting, or include a variable to the filename (such as the build number or timestamp) to ensure that each filename is unique.
- Save your changes.
Next time you run the pipeline, the integration writes a summary report as a JSON file in the location you specified. This report shows the details on discovered, such as:
- Filename
- API UUID assigned for the API when it was uploaded to 42Crunch Platform
- Audit score
- Did the pipeline task fail and if yes, why
- Any errors that occurred when processing the API
Fine-tune the plugin configuration
You can further fine-tune how the integration works by adding a configuration file called 42c-conf.yaml to the root directory of your source code repository where the CI/CD pipeline connects to. You can, for example:
- Configure the plugin to run in the collection mode, applying predefined settings and sharing with teams in your organization on any API collections that it creates.
- Control what happens in the discovery phase.
- Map OpenAPI files in your repository to API UUIDs of APIs in the platform.
- Specify
fail_onconditions to define what the plugin reports as failures.The fail-on criteria you set in the CI/CD plugin, such as the minimum score, are independent from the acceptance criteria defined in security quality gates (SQGs). This means that your CI/CD build can fail either because the criteria of the plugin are not met, the criteria of a SQG are not met, or both.
You can specify different configurations for different branches, tags, or even pull requests. For more details, see the configuration examples in our Resources repository in GitHub.
Configure the integration to use HTTP or HTTPS proxy server
REST API Static Security Testing is powered by Security Audit and connects to 42Crunch Platform when it runs. This is not an issue as long as your Jenkins runs on a machine with direct internet access. However, if you Jenkins is behind an HTTP or HTTPS proxy server, additional configuration is needed.
- Find out and make a note of the address and port of your proxy server.
- In Jenkins, go to Manage Jenkins > Manage Plugins > Advanced.
- Fill in the following settings:
- Server: Host name or address of the proxy server (like
192.168.0.117ormy.proxy.com) - Port: The port that the proxy server listens on (for example,
8090)
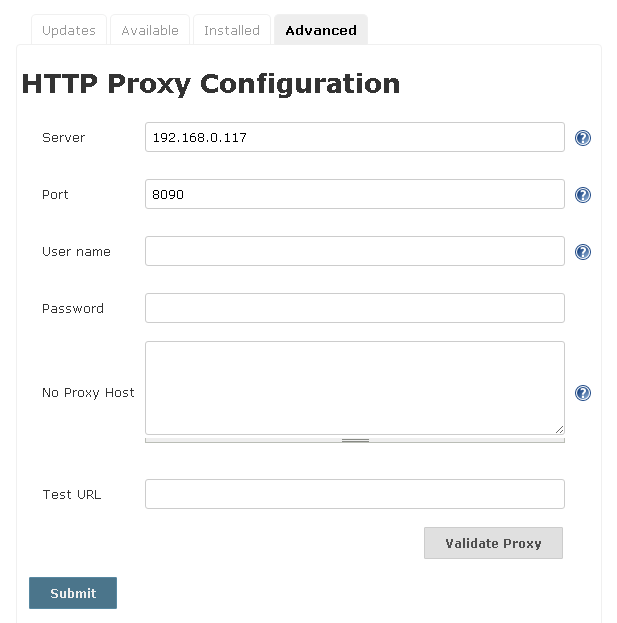
- Server: Host name or address of the proxy server (like
- Click Submit.
Your proxy server configuration is saved. Any new jobs will use it when they run, and REST API Static Security Testing will report that it is using the proxy. If there is something wrong with your proxy configuration, the plugin will fail because requests are not going through.
For more details, see Jenkins Wiki.
Change the default collection name
By default when running on branch, the plugin uses the naming convention <shortened-source-control-uri> Branch:<branch-name> for the created API collection, for example, 42Crunch/sample Branch:sample. However, you can specify a different syntax for the new collections that the plugin uses by default.
- Go to the Jenkins job you want and open the settings of the integration plugin for editing.
- In Default collection name, enter the syntax for the default collection name you want to use. You can use text (like
foo), reference to variables (${repository}), or a combination of the two (foo ${repository}). You can use the following variables that are populated from your repository details:repository: The full repository URL.repo_short_path: A shortened path of the repository URL (the leading/and the trailing.gitare omitted).repo_hostname: The hostname from the repository URL.branch_info:The syntaxBranch:<branch name>, or an empty string if this information is not available.tag_info: The syntaxTag:<tag name>, or an empty string if this information is not available.pr_info: The syntaxPR:<pr id>, or an empty string if this information is not available.
- Save you changes to the settings and to the pipeline.
- Go to the
Jenkinsfileyou want, and open it for editing. - Add the build variable
defaultCollectionNameto the audit stage, and enter the syntax for the default collection name you want to use. You can use text (likefoo), reference to variables (${repository}), or a combination of the two (foo ${repository}). You can use the following variables that are populated from your repository details:repository: The full repository URL.repo_short_path: A shortened path of the repository URL (the leading/and the trailing.gitare omitted).repo_hostname: The hostname from the repository URL.branch_info:The syntaxBranch:<branch name>, or an empty string if this information is not available.tag_info: The syntaxTag:<tag name>, or an empty string if this information is not available.pr_info: The syntaxPR:<pr id>, or an empty string if this information is not available.
- When ready, save your changes.
Next time you run the pipeline, the integration plugin uses the syntax you defined and creates new API collections in 42Crunch Platform (if collections with the same names do not yet exist) where it loads the discovered APIs.
You can also define collection names for specific branches, tags, and pull requests using the property collection_name in the configuration file 42c-conf.yaml.
Set the root directory for the plugin
By default, the integration plugin uses the root directory of your repository as its starting point. However, you can also set a specific directory that the plugin will use as its root.
If you have configured 42c-conf.yaml for your plugin, make sure it is located in the root directory that you want the plugin to use. Otherwise, the configuration file is ignored.
- Go to the Jenkins job you want and open the settings of the integration plugin for editing.
- In Root directory, enter the path of the directory you want to use as the root directory.
- Save your changes.
- Go to the
Jenkinsfileyou want, and open it for editing. - Add the build variable
rootDirectoryto the audit stage, and enter the path of the directory you want to use as the root directory. - Save your changes.
Next time you run the pipeline, the integration plugin will start the discovery phase from the directory path you defined and check that directory and any subdirectories under it for OpenAPI files.
Add tags to APIs
You do not have to wait till your OpenAPI definitions are in 42Crunch Platform to apply tags to them. If you have some tags that you know your APIs need, you can set those tags directly in the CI/CD plugin. The plugin then applies the tags to all new APIs it discovers. For more details, see Tags.
Tags consist of category:tag value pairs, and each tag always has a category it belongs to. Before you start, the categories you want to use must already exist in 42Crunch Platform.
If a tag category allows users to create tags in it, you do not necessarily have to go and create the tags beforehand — in this case, the CI/CD plugin can create any missing tags for you. However, if a tag category does not allow user-created tags, all tags you want to apply must exist before you run your pipeline, otherwise the build task fails. For more details, see Category settings.
- Go to the Jenkins job you want and open the settings of the integration plugin for editing.
- In Set tags for newly created APIs, list the tags that you want the plugin to apply to APIs it discovers. If applying multiple tags, separate each key-value pair with a space. For example, if you would want to apply a tag called
foofromcategory1and a tag calledbarfromcategory2, you would entercategory1:foo category2:bar. - Save your changes.
Category settings may restrict how you can use the tags from a category, such as how many tags from it you can apply to a single API. The CI/CD plugin cannot apply tags from a category that only allows organization administrators to apply tags.
- Go to the
Jenkinsfileyou want, and open it for editing. - Add the build variable
apiTagsto the action, and list the tags that you want the plugin to apply to APIs it discovers. If applying multiple tags, separate each key-value pair with a space. For example, if you would want to apply a tag calledfoofromcategory1and a tag calledbarfromcategory2, you would entercategory1:foo category2:bar.Category settings may restrict how you can use the tags from a category, such as how many tags from it you can apply to a single API. The CI/CD plugin cannot apply tags from a category that only allows organization administrators to apply tags.
- Save your changes.
Next time you run the pipeline, the integration plugin will apply the tags you listed to all new APIs that it discovers in your repository before the APIs are audited. Only newly discovered APIs are tagged: the plugin does not apply tags to APIs it has already uploaded to 42Crunch Platform, nor to any APIs you might have mapped in your 42c-conf.yaml file.
If the CI/CD plugin cannot apply one or more of the tags you have listed, either because the category does not exist or the category settings prevent the plugin from applying using it or creating any missing tags, the plugin fails the build task. If this happens, you can:
- Remove the tags that cause the failure from the plugin configuration.
- Ask you organization administrators to change the settings of the tag categories that are causing the problem.
- Ask your organization administrators to create any missing tags that you need.
Tags created through the CI/CD plugin do not have descriptions, but organization administrators can update the tags to add one.
Use SQG criteria instead of plugin configuration
By default, the integration plugin configuration defines when the CI/CD task passes or fails, and there are some default values that the plugin uses if nothing else is specified. However, if you are using security quality gates (SQGs) in 42Crunch Platform for quality control, you might prefer SQGs to determine when the CI/CD task passes or fails. In this case, you can set the plugin to skip the locally defined fail-on conditions (such as minimum score, format validity, or forbidden issues) and only use those defined in the SQGs.
- Go to the Jenkins job you want and open the settings of the integration plugin for editing.
- Select Skip local checks, and save your changes.
- Go to the
Jenkinsfileyou want, and open it for editing. - Add the build variable
skipLocalChecksto the audit stage, and set it totrue. - Save your changes.
Next time you run the pipeline, the plugin will only check the status of all SQGs applied to the APIs it found in the repository when deciding if the build passes or fails, and ignore any fail-on conditions defined in the plugin itself, including the default plugin configuration.
Stop the plugin from failing a pipeline
Sometimes you might want the CI/CD plugin just to report the found issues, not block the pipeline from continuing. For example, your repository might have plenty of APIs in early stages of their lifecycle, or you have just introduced the CI/CD plugin to the pipeline and need time to adjust to the set quality criteria. In this case, you can temporarily switch off all fail-on conditions that the CI/CD plugin would impose on a CI/CD job. The plugin keeps reporting on the discovered APIs but does not block the pipeline from proceeding to subsequent stages.
Switching off the fail-on conditions in the CI/CD plugin means that the plugin will cease to work as a quality control as it will never prevent potential problems in your APIs. We recommend that you use this option only after a careful consideration and only for a limited time. Remember to remove this setting from the plugin as soon as possible.
- Go to the Jenkins job you want and open the settings of the integration plugin for editing.
- Select Force ignore all failures, and save your changes.
- Go to the
Jenkinsfileyou want, and open it for editing. - Add the build variable
IgnoreFailuresto the audit stage, and set it totrue. - Save your changes.
Next time you run the pipeline, the integration plugin runs normally, uploading each discovered API definition and its audit report to 42Crunch Platform, but does not fail the CI/CD job because of the audit results or SQG status. However, the plugin still produces logs as per usual, so you can check them to see the status of the discovered APIs.
Ignore network errors
If you are worried that issues in connectivity — such as in the rare case of the CI/CD plugin not being able to communicate to 42Crunch Platform — could unduly hinder an important CI/CD pipeline by causing it to fail, you can set the plugin to ignore connectivity issues.
Setting the CI/CD plugin to ignore network errors lessens the plugin's effectivity as a quality control, because the task does not stop the CI/CD pipeline even though it could not complete successfully due to a connectivity issue. This means that APIs that have quality or security issues in their OpenAPI definitions could slip through upon a successful CI/CD job. We recommend that you use this option only after a careful consideration.
- Go to the Jenkins job you want and open the settings of the integration plugin for editing.
- Select Force ignore network failures, and save your changes.
- Go to the
Jenkinsfileyou want, and open it for editing. - Add the build variable
ignoreNetworkErrorsto the audit stage, and set it totrue. - Save your changes.
Next time you run the pipeline, if the integration plugin encounters a connectivity issue, it does not fail the CI/CD job and the pipeline proceed to subsequent steps. Errors that cannot be definitively deemed to be connectivity issues will still cause the plugin to fail the job. You can check the logs that the plugin produces to see if any errors occurred.
What is...
How to...
Integrate CI/CD solutions with 42Crunch Platform
Integrate Security Audit with Azure Pipelines
Integrate Security Audit with Bamboo
Integrate Security Audit with Bitbucket Pipelines
Integrate Security Audit with CI/CD using a Docker image