42Crunch Platform release, May 7, 2025
|
Platform version: v1.45.x |
This 42Crunch API Security Platform release expands the CI/CD plugin configuration with collection mode and sharing with teams, and provides several smaller improvements.
New features
The following are the new features and improvements to the existing ones in this release.
Collection mode and team sharing in CI/CD plugins
You can now use the 42c-conf.yaml file to configure your REST API Static Security Testing plugin to run in collection mode in the discovery phase:
- Specify the names for API collections that the plugin creates and uploads APIs to.
- Set the plugin to automatically share the API collections with specific teams in your organization and what access level each team has on the collection.
- Define separate behavior for different directories in your source code repository, or create a default collection mode configuration. If a branch, directory, tag, or PR has a specific configuration defined for it, this configuration overrides the default one.
Automatic sharing with teams is only available in the collection mode and only applies to new API collections that are created. The sharing of already existing API collections is not changed.
For more details on the collection mode and how to use 42c-conf.yaml, see Further configuration with 42c-conf.yaml and the configuration examples in our Resources repository in GitHub.
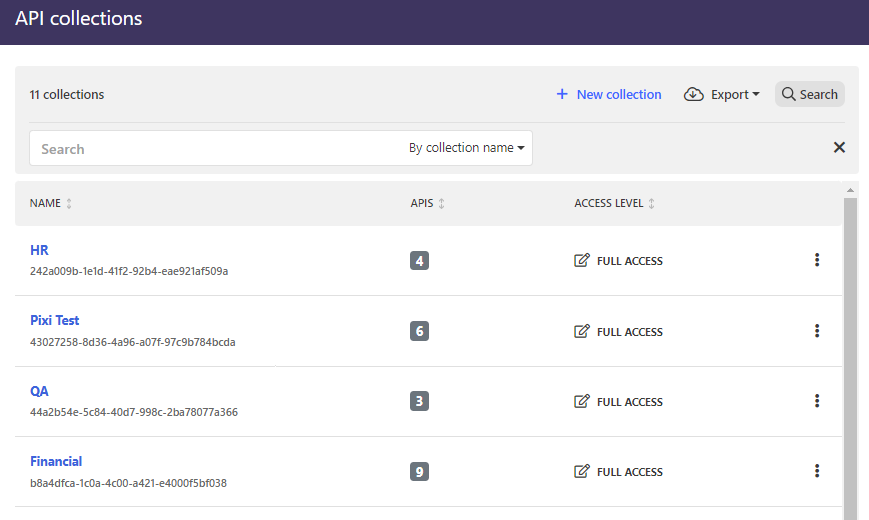
API collection UUIDs in the collection list
The API collection UUIDs are now clearly visible on the UI in the list of API collections, and you can easily copy the UUID if you need to provide it to someone.
Copying the collection UUID is also available inside every API collection:
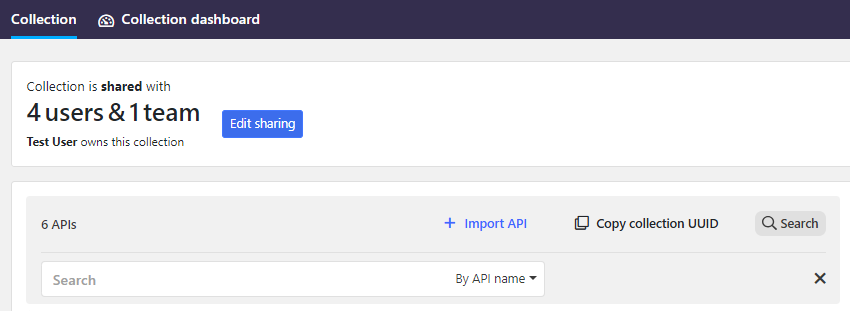
For more details on API collections, see API collections.
More details on tags in the platform audit logs
When logging events related to tags, such as assigning or unassigning tags to an API, platform audit logs now also log the name of the tag in question, to provide more context on these actions.
For more details, see Platform audit logs.
User names always shown in the team list
Previously, in the rare case that users did not have first and last names defined in their user profiles (either because of SSO configuration or because they had removed them later), it might have been hard to spot these users in the lists of team members because the column for the name was empty and the email address uses less visible font.
We have now improved the user creation so that the first and last names would always be included by default. If the first and last names are not available, the user email is now repeated also in the name column, making it easier to spot the right user and making it more visible that the names are missing.
Compatibility
This section lists the compatible Docker images for some of the components of 42Crunch API Security Platform, as well as other possible compatibility details.
API Firewall images
This release is compatible with the following API Firewall images:
-
42crunch/apifirewall:v1.1.9- Upgrade to
expat 2.7.0-r0(CVE-2024-8176) - Upgrade to
golang.org/x/net 0.36.0(CVE-2025-22870)
- Upgrade to
42crunch/apifirewall:v1.1.8- Upgrade to
openssl-3.3.3(CVE-2024-12797, CVE-2024-13176)
- Upgrade to
42crunch/apifirewall:v1.1.7- Fixed the failure in forwarding large request bodies
- Upgrade to
go-1.23.4(CVE-2024-45338)
-
42crunch/apifirewall:v1.1.6- Upgrade to
openssl-3.3.2-r1(CVE-2024-9143)
- Upgrade to
42crunch/apifirewall:v1.1.5- Switch to the system certificate store to fix certificate authority renewal issue
All previous image versions have been deprecated and are no longer supported. We highly recommend that you switch to the latest image version to take the full advantage of the new features and security improvements.
When you switch the version of the API Firewall image, you must reconfigure any existing protection configurations so that they work with the new version. For more details, see Reconfigure API Protection.
API Scan images
This release is compatible with the following API Scan images for running it on-premises.
We have aligned the scan image version numbering with the version of the platform release, and from now on the minor version number (here .45) will be the same as the platform release. The major release number will still indicate if the image is for Scan v1 or Scan v2.
Scan v2
- NEW:
42crunch/scand-agent:v2.45.0- Upgrade to
Golang 1.24.2(CVE-2025-22871) - Upgrade to
golang.org/x/net v0.39.0(CVE-2025-22872)
- Upgrade to
We highly recommend that you switch to the latest image version to take full advantage of the new features and security improvements.
-
42crunch/scand-agent:v2.0.21- Support for OWASP API Security Top 10 2023
- Sub-schemas from
anyOfconstructions excluded from testing - Improved generation of Boolean values in tests
- Upgrade to
golang-jwt/jwt/v5 v5.2.2(CVE-2025-30204) - Upgrade to
go-redis/v9 v9.7.3(CVE-2025-29923) - Upgrade to
kin-openapi v0.131.0(CVE-2025-30153)
42crunch/scand-agent:v2.0.20- Fixed response validation on arrays
- Upgrade to
golang.org/x/net v0.37.0(CVE-2025-22870)
42crunch/scand-agent:v2.0.19- Initial support for the OAS v3.1 in API Scan
- Improved
.p12support - Upgrade to
golang.org/x/oauth2 v0.25.0(CVE-2025-22868) - Upgrade to
golang.org/x/crypto v0.33.0(CVE-2025-22869)
42crunch/scand-agent:v2.0.18- Fixed handling of empty scenario list in the lax scanning mode
- Increased maximum number of items in generated arrays
42crunch/scand-agent:v2.0.17- Upgrade to
go-git v5.13.1(CVE-2025-21613, CVE-2025-21614) - Upgrade to
nanoid v3.3.8(CVE-2024-55565) - Upgrade to
golang.org/x/net v0.33.0(CVE-2024-45338) - Upgrade to
golang.org/x/crypto v0.31.0(CVE-2024-45337)
- Upgrade to
-
42crunch/scand-agent:v2.0.15- Fixed replacement of placeholder texts in variables when generating test requests
- Fixed generation of properties in test requests
- Fixed regression on
nullenums
-
42crunch/scand-agent:v2.0.13- A new property in the scan report to indicate if running a scan test succeeded or not
42crunch/scand-agent:v2.0.12- Fixed scan report timestamp
42crunch/scand-agent:v2.0.11- Upgrade to
Golang v1.23.1(CVE-2022-30635, CVE-2024-34155, CVE-2024-34156, CVE-2024-34158)
- Upgrade to
42crunch/scand-agent:v2.0.10- New test
response-body-badformat-scan - Fixed scan configuration creation when
itemsisnull - Fixed excessive data exposure reporting
- New test
42crunch/scand-agent:v2.0.9- Scan v2 in v1-compatible mode
- Support for
Acceptheaders - Upgrade to
Golang 1.22.5(CVE-2024-24789, CVE-2024-24790, CVE-2024-24791)
42crunch/scand-agent:v2.0.8- New test
path-item-method-not-allowed-no-authn-scan - Support for
apiConnectivityCheck,maxTimeoutRetryAttempts, andrequestHeaderNameRequestType - Fixed implementation of
reportIncludeRequestBodyandreportIncludeResponseBody - Fixed handling of lookahead and lookbehind assertion references in regular expressions
- New test
42crunch/scand-agent:v2.0.7- Upgrade to
Golang 1.22.3(CVE-2020-8559, CVE-2024-24788)
- Upgrade to
42crunch/scand-agent:v2.0.6- Lax testing mode
- Fixed generating conformance test requests when multiple required properties are defined
42crunch/scand-agent:v2.0.4- Numeric values exceeding the limits of
float64presented as strings
- Numeric values exceeding the limits of
42crunch/scand-agent:v2.0.3- Upgrade to
Golang 1.21.5(CVE-2023-45284, CVE-2023-45283, CVE-2023-39326, CVE-2023-45283) - New scan report
- Tests
parameter-header-contenttype-wrong-scanandpartial-security-accepted - Support for
reportIncludeRequestBody,reportIncludeResponseBody,reportMaxRequestSizeHappyPath,reportMaxRequestSizeTest - Improved logging for runtime limit
- Heartbeat check
- Upgrade to
All previous image versions have been deprecated and are no longer supported.
Scan v1
- NEW:
42crunch/scand-agent:v1.45.0- Upgrade to
Golang 1.24.2(CVE-2025-22871) - Upgrade to
golang.org/x/net v0.39.0(CVE-2025-22872)
- Upgrade to
We highly recommend that you switch to the latest image version to take full advantage of the new features and security improvements.
42crunch/scand-agent:v1.22.27- Support for OWASP API Security Top 10 2023
- Sub-schemas from
anyOfconstructions excluded from testing - Improved generation of Boolean values in tests
- Upgrade to
golang-jwt/jwt/v5 v5.2.2(CVE-2025-30204) - Upgrade to
go-redis/v9 v9.7.3(CVE-2025-29923) - Upgrade to
kin-openapi v0.131.0(CVE-2025-30153)
42crunch/scand-agent:v1.22.25- Initial support for the OAS v3.1 in API Scan
- Improved
.p12support - Upgrade to
golang.org/x/oauth2 v0.25.0(CVE-2025-22868) - Upgrade to
golang.org/x/crypto v0.33.0(CVE-2025-22869)
-
42crunch/scand-agent:v1.22.24- Fixed handling of nullable enums and empty strings
- Increased maximum number of items in generated arrays
42crunch/scand-agent:v1.22.23- Upgrade to
go-git v5.13.1(CVE-2025-21613, CVE-2025-21614) - Upgrade to
nanoid v3.3.8(CVE-2024-55565) - Upgrade to
golang.org/x/net v0.33.0(CVE-2024-45338) - Upgrade to
golang.org/x/crypto v0.31.0(CVE-2024-45337)
- Upgrade to
42crunch/scand-agent:v1.22.21- Default value maximum scan report size 20 MB to align with Scan v2
42crunch/scand-agent:v1.22.20- Fixed excessive data exposure reporting
42crunch/scand-agent:v1.22.19- Upgrade to
Golang v1.23.1(CVE-2022-30635, CVE-2024-34155, CVE-2024-34156, CVE-2024-34158) - Happy path tests included in the number of tests
- Upgrade to
42crunch/scand-agent:v1.22.18- Fixed scan configuration creation when
itemsisnull
- Fixed scan configuration creation when
42crunch/scand-agent:v1.22.17- Upgrade to
Golang 1.22.5(CVE-2024-24789, CVE-2024-24790, CVE-2024-24791)
- Upgrade to
42crunch/scand-agent:v1.22.16- Upgrade to
Golang 1.22.3(CVE-2020-8559, CVE-2024-24788)
- Upgrade to
42crunch/scand-agent:v1.22.15- Fixed handling of query parameters in request generation
- Fixed generating conformance test requests when multiple required properties are defined
42crunch/scand-agent:v1.22.14- Upgrade to
Golang 1.21.5(CVE-2023-39326, CVE-2023-45283)
- Upgrade to
42crunch/scand-agent:v1.22.13- Upgrade to
Golang 1.21.3(CVE-2023-45284, CVE-2023-45283) - Heartbeat check to keep the connection to 42Crunch Platform active in case of extremely long scans
- Fixed handling of
exampleandx-42c-sample
- Upgrade to
42crunch/scand-agent:v1.22.12- Support for
text/plainas content type - Support for
read-onlyproperties
- Support for
-
42crunch/scand-agent:v1.22.11- Upgrade to
Golang 1.20.7(CVE-2023-39319, CVE-2023-39318, CVE-2023-3978, CVE-2023-29409) - Fixed handling of
<and>characters in the request payload - Improved handling of content not supported by API Scan
- Upgrade to
42crunch/scand-agent:v1.22.9- Performance improvements to scan configuration generation
- Better memory handling when generating array items of the type
filefor scan requests - Better handling of expired customization rules
- Improved JSON schema validation for UTF-8 strings
42crunch/scand-agent:v1.22.8- Upgrade to
Golang 1.20.4(CVE-2022-41716, CVE-2022-41717, CVE-2022-41720, CVE-2022-41722, CVE-2022-41723, CVE-2022-41724, CVE-2022-41725, CVE-2023-24532, CVE-2023-24534, CVE-2023-24536, CVE-2023-24537, CVE-2023-24538, CVE-2023-24539, CVE-2023-24540, CVE-2023-29400)
- Upgrade to
42crunch/scand-agent:v1.22.7- Updates to regular expression library
42crunch/scand-agent:v1.22.6- Fixed regular expressions handling
In some rare cases, certain regular expression patterns could send the on-premises scan to an infinite loop, and the process would not finish. This image version fixes that, so if you are experiencing on-premises scan hanging, we recommend upgrading from the previous scan images to this one.
- Fixed regular expressions handling
42crunch/scand-agent:v1.22.4- Improved array iteration
All previous image versions have been deprecated and are no longer supported.
Changed behavior
In addition to the well-defined format of date-time, Security Audit no longer raises issues about missing maxLength or pattern on strings where format is date,
time, duration, or ipv6 (RFC 3339). Depending on your API, this may affect the audit score.
Known issues
This release has the following known issues.
OWASP API Security Top 10 2023 not in security quality gates
The OWASP API Security Top 10 vulnerabilities are not yet included as fail-on conditions in security quality gates (SQGs). This will be fixed in the next release.
Manage teams permission not shown on list of users
The permission to manage teams is not yet shown on the list of users in your organization, but you can view all permissions that a user has by clicking the permission column. This permission also does not yet have a shortcut that you could use when searching by permission.
These will be fixed in a future release.
Changing tagging on an API may trigger an unrelated error on the UI
Sometimes applying tags to or removing them from an API may trigger an unrelated error on failing to fetch the SQG approval report for the API. This happens if the API in question has been scanned on-premises and the scan has finished after you arrived on the API Summary page, because the UI cannot find the latest on-premises scan report and the associated approval report. Refreshing the page gets the latest reports and resolves the issue.
Tagging and untagging the API is not affected by this error: tags get correctly applied and removed in any case.
This will be fixed in a future release.
Data dictionary duplication
Duplicating a data dictionary does not yet duplicate the values in it.
This will be fixed in a future release.
Scan customization rules may lead to no response codes being accepted.
In some cases, scan rules can lead to HTTP status response codes in API responses that are normally expected (for example, HTTP 401 or HTTP 404) to be treated as unexpected. This in turn can lead to a false positive in the scan results.
By default, the expected HTTP status response codes that are defined in scan rules applied to the scanned API take preference over the response codes that API Scan would otherwise expect. However, this can cause problems in scan process if your scan rule only skips header or response body analysis but does not define any expected response codes, either for happy path requests or for particular test IDs. This results in the scan rule to have null defined as the expected response code, and because the scan rule takes preference over the default scan behavior, no response codes except null are accepted. This in turn means that some tests are incorrectly flagged as returning unexpected response codes when they were in fact successful.
We are currently investigating the best way how to reconcile the designed behavior of API Scan and scan rules in these cases, and this issue will be fixed in a future release.