42Crunch Platform release, February 6, 2024
|
Platform version: v1.32.x |
This 42Crunch API Security Platform release introduces scan playbooks and improves support for mutual TLS as an authentication method in Security Audit.
New features
The following are the new features and improvements to the existing ones in this release.
Improvements to Conformance Scan
For both scan versions, we have clarified the texts on the scan tile on API summary tab, and when configuring a scan security quality gate (SQG).
Improvements to Scan v2
We have introduced scan playbooks in Scan v2 configurations to make viewing your scan scenarios easier. A playbook compiles all scan scenarios in a particular scan configuration together so that you can browse through them and check their details. Scan playbook also makes the chain and order of requests that are executed in a scenario
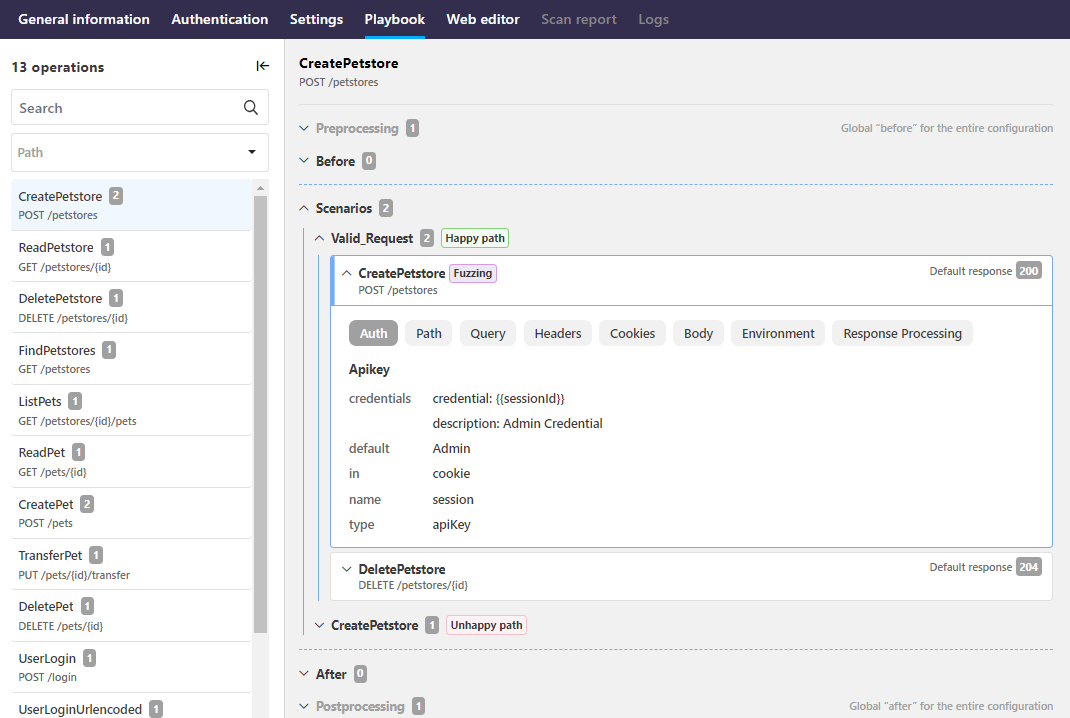
For more details, see Scan scenarios and playbooks.
In addition, the scan v2 report now includes more details on the scan results:
- Failed happy path requests now provide the reason for the failure:

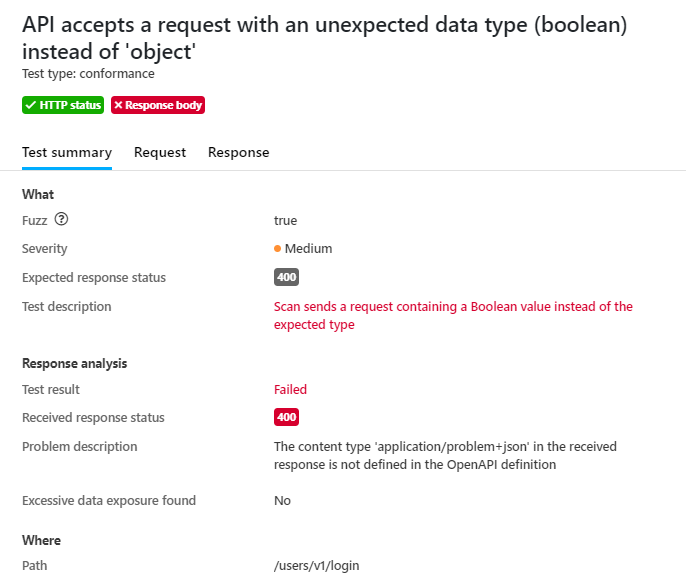
- When the received HTTP status code is ok but the response body fails, more details on the problem are provided in the report:
We have also fixed how the scan handles headers that have not been marked as required.
Improvements to Scan v1
We have fixed the password validation when configuring mutual TLS (mTLS) in the scan configuration.
Improved support for mTLS in Security Audit
We have improved how Security Audit handles the extension x-42c-mtls:
- If you add the extension
x-42c-mtlsto your API to indicate that it uses mTLS for the authentication, Security Audit considers your API to be fully protected and does not deduct points from your security. The audit still reports any potential security issues it found so that you can take them into account when developing your API further. - You can now also declare the use of mTLS as an audit rule to easily apply the extension on the global level. If only some operations in your API use mTLS, it is better to apply the extension to individual API operations directly in the API definition.
Mutual TLS can only be considered secure if connections are over HTTPS, not if traffic is in the clear over HTTP. If you have declared mTLS with x-42c-mtls but server (OAS v3) or schemes (OAS v2) objects define http, Security Audit ignores x-42c-mtls and security issues deduct points normally.
You cannot apply x-42c-mtls, x-42c-accept-empty-security, or x-42c-no-authentication (either from audit rules or as extensions directly in the API definition) to the same API. This would lead to Security Audit getting conflicting directives for authentication checks so that it could not reliably process the API.
For more details, see x-42c-mtls.
Compatibility
This section lists the compatible Docker images for some of the components of 42Crunch API Security Platform, as well as other possible compatibility details.
API Firewall images
This release is compatible with the following API Firewall images:
42crunch/apifirewall:v1.0.25- Upgrade to
go-1.21.1(CVE-2023-39319, CVE-2023-39318, CVE-2023-3978, CVE-2023-29409) - Upgrade to
openssl-1.1.1w(CVE-2023-4807, CVE-2023-3817, CVE-2023-3446)
- Upgrade to
42crunch/apifirewall:v1.0.24- Upgrade to
httpd-2.4.57(CVE-2023-25690, CVE-2023-27522) - Upgrade to
openssl-1.1.1u(CVE-2023-2650, CVE-2023-0465, CVE-2023-0466, CVE-2023-0464) - Support for multiple API key security schemes with the same name
- Fixed the handling of content
media-typedeclared as opaque string in response validation - Fixed request body handling when API Firewall is set to non-blocking mode.
- Obfuscated headers (except
Host) in transaction logs when the targeted API is unknown - New versions of JWT validation protections (
x-42c-jwt-validation-ec_0.2,x-42c-jwt-validation-rsa_0.2,x-42c-jwt-validation-hmac_0.2)- Validating the
scopeclaim of OAuth2 JWT tokens - Connecting to the JWKS server through a remote forward proxy
- Validating the
- Upgrade to
42crunch/apifirewall:v1.0.23- Health check over SSL
- The environment variable
PLATFORM_HOST - Fixed the handling of
multipart/form-datarequests - Upgrade to
openssl-1.1.1t - Upgrade to
httpd-2.5.55 -
Upgrade to
apr-util-1.6.3
42crunch/apifirewall:v1.0.22- Fixed JWT signature validation
- Allowed plain string content definition
- Upgrade to
openssl-1.1.1s - Upgrade to
libexpat 2.5.0 - Upgrade to
libapreq 2.17 - Upgrade to
libjansson 2.14 - Upgrade to
libjose 11 - Upgrade to
libmaxminddb 1.7.1
42crunch/apifirewall:v1.0.21- Fixed
contenthandling in non-body parameters - HTTP status response code synchronization with Conformance Scan default expectations
- Fixed
42crunch/apifirewall:v1.0.20- Upgrade to
openssl-1.1.1o(CVE-2022-2274, CVE-2022-2097) - Fixed decreasing the number of active instances when firewall shuts down abruptly
- Upgrade to
42crunch/apifirewall:v1.0.19- Upgrade to
httpd-2.4.54(CVE-2022-26377, CVE-2022-28330, CVE-2022-28614, CVE-2022-28615, CVE-2022-29404, CVE-2022-30522, CVE-2022-30556, CVE-2022-31813)
- Upgrade to
42crunch/apifirewall:v1.0.18- Upgrade to
openssl-1.1.1o(CVE-2022-0778, CVE-2022-1292, CVE-2022-1343, CVE-2022-1434, CVE-2022-1473) - Proper handling of the properties
readOnlyandwriteOnlyfrom the OpenAPI Specification (OAS) in schemas
- Upgrade to
All previous image versions have been deprecated and are no longer supported.
Conformance Scan images
This release is compatible with the following Conformance Scan images for running it on-premises.
Scan v2
42crunch/scand-agent:v2.0.5- Fixed handling of unrequired headers
We highly recommend that you switch to the latest version to take the full advantage of the new features and security improvements.
42crunch/scand-agent:v2.0.4- Numeric values exceeding the limits of
float64presented as strings
- Numeric values exceeding the limits of
42crunch/scand-agent:v2.0.3- Upgrade to
Golang 1.21.5(CVE-2023-45284, CVE-2023-45283, CVE-2023-39326, CVE-2023-45283) - New scan report
- Tests
parameter-header-contenttype-wrong-scanandpartial-security-accepted - Support for
reportIncludeRequestBody,reportIncludeResponseBody,reportMaxRequestSizeHappyPath,reportMaxRequestSizeTest - Improved logging for runtime limit
- Heartbeat check
- Upgrade to
42crunch/scand-agent:v2.0.2- Support for
text/plainas content type - Support for
read-onlyproperties
- Support for
42crunch/scand-agent:v2.0.1- Upgrade to
Golang 1.20.7(CVE-2023-39319, CVE-2023-39318, CVE-2023-3978, CVE-2023-29409) - Enhancements to generating random values from scan configuration
- Tests for not allowed methods are omitted if a
beforeblock on a global level in the scan configuration is failing, or the scan configuration is set to run happy path tests only
- Upgrade to
42crunch/scand-agent:v2.0.0- The new version of Conformance Scan
All previous image versions have been deprecated and are no longer supported.
Scan v1
42crunch/scand-agent:v1.22.14- Upgrade to
Golang 1.21.5(CVE-2023-39326, CVE-2023-45283)
- Upgrade to
42crunch/scand-agent:v1.22.13- Upgrade to
Golang 1.21.3(CVE-2023-45284, CVE-2023-45283) - Heartbeat check to keep the connection to 42Crunch Platform active in case of extremely long scans
- Fixed handling of
exampleandx-42c-sample
- Upgrade to
42crunch/scand-agent:v1.22.12- Support for
text/plainas content type - Support for
read-onlyproperties
- Support for
-
42crunch/scand-agent:v1.22.11- Upgrade to
Golang 1.20.7(CVE-2023-39319, CVE-2023-39318, CVE-2023-3978, CVE-2023-29409) - Fixed handling of
<and>characters in the request payload - Improved handling of content not supported by Conformance Scan
- Upgrade to
42crunch/scand-agent:v1.22.9- Performance improvements to scan configuration generation
- Better memory handling when generating array items of the type
filefor scan requests - Better handling of expired customization rules
- Improved JSON schema validation for UTF-8 strings
42crunch/scand-agent:v1.22.8- Upgrade to
Golang 1.20.4(CVE-2022-41716, CVE-2022-41717, CVE-2022-41720, CVE-2022-41722, CVE-2022-41723, CVE-2022-41724, CVE-2022-41725, CVE-2023-24532, CVE-2023-24534, CVE-2023-24536, CVE-2023-24537, CVE-2023-24538, CVE-2023-24539, CVE-2023-24540, CVE-2023-29400)
- Upgrade to
42crunch/scand-agent:v1.22.7- Updates to regular expression library
42crunch/scand-agent:v1.22.6- Fixed regular expressions handling
In some rare cases, certain regular expression patterns could send the on-premises scan to an infinite loop, and the process would not finish. This image version fixes that, so if you are experiencing on-premises scan hanging, we recommend upgrading from the previous scan images to this one.
- Fixed regular expressions handling
42crunch/scand-agent:v1.22.4- Improved array iteration
All previous image versions have been deprecated and are no longer supported.
Known issues
This release has the following known issues.
Only reference scan configuration shows SQG status in the scan report
Currently, the scan report summary shows the SQG status for only on the report of the reference scan configuration. When viewing other reports, the scan summary incorrectly shows that the API would not have any SQGs applied to it. However, SQGs are still being correctly applied and the SQG status correctly shown for each report in the list of scan reports.
This will be fixed in a future release.
Manage teams permission not shown on list of users
The permission to manage teams is not yet shown on the list of users in your organization, but you can view all permissions that a user has by clicking the permission column. This permission also does not yet have a shortcut that you could use when searching by permission.
These will be fixed in a future release.
Changing tagging on an API may trigger an unrelated error on the UI
Sometimes applying tags to or removing them from an API may trigger an unrelated error on failing to fetch the SQG approval report for the API. This happens if the API in question has been scanned on-premises and the scan has finished after you arrived on the API Summary page, because the UI cannot find the latest on-premises scan report and the associated approval report. Refreshing the page gets the latest reports and resolves the issue.
Tagging and untagging the API is not affected by this error: tags get correctly applied and removed in any case.
This will be fixed in a future release.
Data dictionary duplication
Duplicating a data dictionary does not yet duplicate the values in it.
This will be fixed in a future release.
Scan customization rules may lead to no response codes being accepted.
In some cases, scan rules can lead to HTTP status response codes in API responses that are normally expected (for example, HTTP 401 or HTTP 404) to be treated as unexpected. This in turn can lead to a false positive in the scan results.
By default, the expected HTTP status response codes that are defined in scan rules applied to the scanned API take preference over the response codes that Conformance Scan would otherwise expect. However, this can cause problems in scan process if your scan rule only skips header or response body analysis but does not define any expected response codes, either for happy path requests or for particular test IDs. This results in the scan rule to have null defined as the expected response code, and because the scan rule takes preference over the default scan behavior, no response codes except null are accepted. This in turn means that some tests are incorrectly flagged as returning unexpected response codes when they were in fact successful.
We are currently investigating the best way how to reconcile the designed behavior of Conformance Scan and scan rules in these cases, and this issue will be fixed in a future release.