42Crunch Platform release, May 18, 2021
This 42Crunch API Security Platform release adds the repository details in API collections created through CI/CD pipelines, as well as stricter pattern validation and new checks to API Security Audit.
New features
The following are the new features and improvements to the existing ones in this release.
Repository information on API collections
API collections that are created through the REST API Static Security Testing plugin now show which repository and branch they were created from. Each API in these collections also shows the file path of the API in your repository.
For more details, see CI/CD integration.
In addition, a bug prevented organization administrators from seeing all API collections in their organization if they made an API call to list the collections, for example, using our CLI client and authenticated with API key. This has now been fixed, and organization administrators can again see all API collections in their organization, even when making an API call with API key.
Stricter validation for loose patterns and new checks in Security Audit
To increase security, we have made the validation of loose patterns for strings stricter, as weak patterns offer no protection in runtime. Security Audit now also captures regular expressions based on meta-characters that do not properly constrain the charset in strings, such as ., \S, and [\s\S], to name but a few.
Security Audit also has new checks response-406 and v3-response-406 to check that the HTTP 406 response is defined for all GET, POST, PUT, PATCH, and DELETE operations in your OpenAPI definition. For more details, see:
Both of the changes above may affect your APIs' score on data validation.
API Security Encyclopedia is now included as part of the platform documentation, and you can use the search to find the issue ID you want.
New UX improvements
In addition, there are also several smaller improvements to the user experience:
- Find API now properly handles incorrect API UUIDs
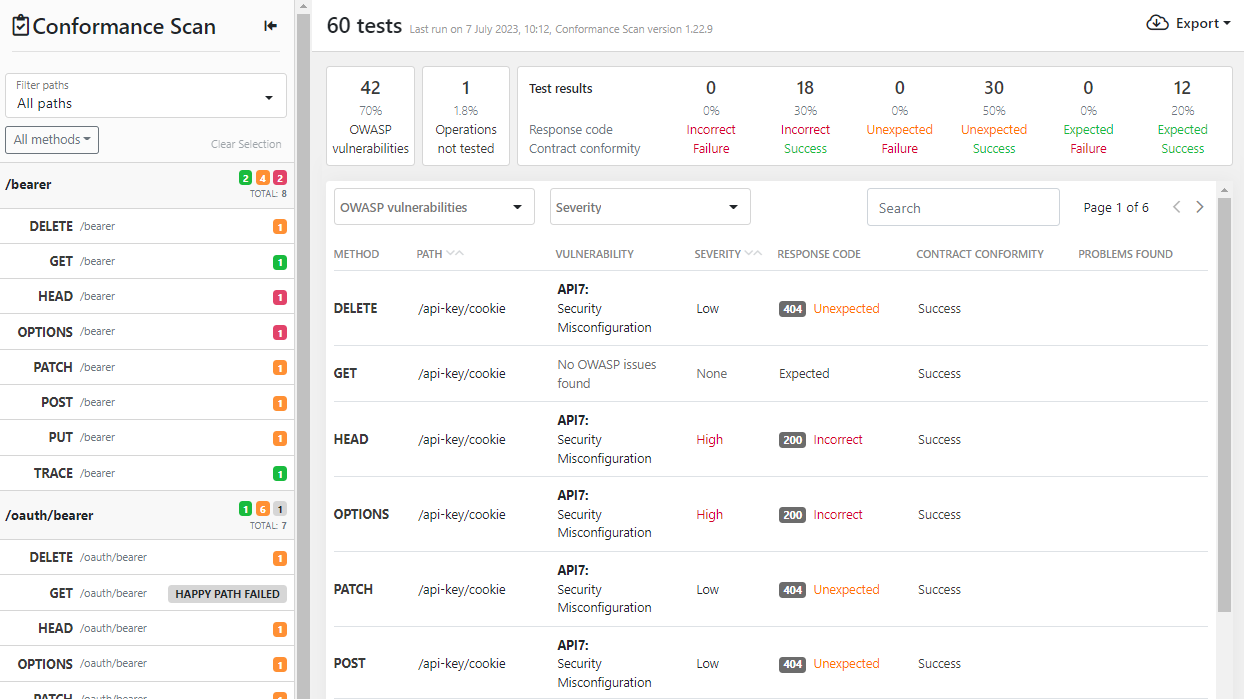
- Scan report now splits the test that scan ran and the issue it found into separate columns:
- Access rights that you can give for API tokens are now grouped according to type
- Improved error messages
New versions of CI/CD plugins
All of our REST API Static Security Testing CI/CD plugins have been updated. The main changes include:
- On subsequent runs of the plugin, the contents of the APIs in platform are replaced with the contents of the API files in your repository to keep them in sync, but the existing API UUIDs are retained. This means that history of the APIs, for example, existing scan reports, is retained too.
- You can now specify default sharing options for any new API collection that the plugin creates. As before, you can also change the sharing and access levels of the API collections in 42Crunch Platform after they have been created.
- You can now fine-tune different branches in your repository independently. The plugin configuration file
42c-conf.yamllets you define different conditions and behavior per branch. You can also use wildcards for the branch names in the file if you want to apply a configuration to multiple branches at one go.
For more details, see CI/CD integration.
Postman collection for Security Audit
We have created a Postman collection so you can now run Security Audit directly in Postman. The collection includes API requests to create an API collection, import an OpenAPI definition, and to show an audit report in Postman. If you use Postman's Collection Runner, you can do all this with one click. For more details, see the documentation of the Postman collection.
Compatibility
This section lists the compatible Docker images for some of the features of 42Crunch API Security Platform, as well as other possible compatibility details.
API Firewall images
This release is compatible with the following API Firewall images:
42crunch/apifirewall:v1.0.6- Fixed blocking query parameters that are not defined in the API definition of the protected API.
- Fixed invalid decoding of
multipart/form-data.
42crunch/apifirewall:v1.0.5- Upgrade to
openssl-1.1.1k(CVE-2021-3450, CVE-2021-3449).
- Upgrade to
42crunch/apifirewall:v1.0.4- Compatibility with the new platform.
- Improved error messages on unrecoverable errors.
- Fixed memory leak on restart (schema regex).
- Fixed possible crash with large response bodies.
- Improved the engine performance of regular expressions.
- Fixed the handling of
form-dataandx-www-form-urlencodedpayloads with OAS v3. - Harmonized console logs.
- Support for sending logs to STDOUT.
All previous image versions have been deprecated and are not compatible with this version of the platform.
When you switch the version of the API Firewall image, you must reconfigure any existing protection configurations so that they work with the new version. For more details, see Reconfigure API Protection.
API Scan images
This release is compatible with the following API Scan images for running it on-premises:
42crunch/scand-agent:v1.7.4- Fixed handling of
multipleOfwhen its range is[0;0.50].
- Fixed handling of
42crunch/scand-agent:v1.6.0- This version replaces
42crunch/scand-agent:v1.5.2-bugfix01. - Environment variables for communication through proxy to both platform and APIs.
- Scan handles
nullvalue in API response.
- This version replaces
42crunch/scand-agent:v1.5.1- New test
partial_security_acceptedfor testing how missing security requirements are handled. - TLS configuration allows a remote server to repeatedly request renegotiation.
- Improved handling of slashes (
/) and wildcards likeapplication/*in test requests and JSON encoder. - Masked credentials and other small improvements in scan logs.
- More details shown when a happy path request fails
- Improved generation of strings, numbers, integers, and arrays.
- Support for proxy configuration.
- New test
Known issues
This release has the following known issues.
UI bug on sharing new API collections
Currently, when importing APIs to a new API collection in 42Crunch Platform, the UI shows options to share the API collection to all users, even to users who do not have permissions to share API collections. However, what permissions users have remains unchanged on the backend-side. If users who do not have the correct permissions try to share the API collection they create during API import, they get an error, and the import and creating the API collection fails.
This will be fixed in the next release.
Security Audit does not verify the format of vendor extensions
At the moment, Security Audit does not verify that you have used the correct format for vendor extensions to the OpenAPI Specification (OAS). According to the OAS, the field names of vendor extensions must begin with x-. However, Security Audit does not flag it as an error if the field name is missing the x-.
This will be fixed in a future release.
API Scan string limits may conflict with minLength or maxLength values
By default, API Scan limits the maximum length for strings in the requests it sends during the scan to 4096. If the properties minLength or maxLength or the length limits in a regular expression that you have defined for an API operation in your API definition conflict with this limit, it causes issues during the scan.
If the minimum length required is longer than the string length limit allowed in API Scan, the scan cannot create the happy path request for that operation to establish a baseline. If the maximum length allowed in the API is longer than the allowed string length limit in API Scan, the scan can create the happy path request but not the actual request during the scan.
In both cases, the operation is shown as a skipped operation in the scan report, but for different reasons. You must fix the operation in your API definition before it can be successfully scanned.
We are working to improve this in the future.